Hosting

System - Meta RobotsThe HTML head element is the backbone of your Joomla 5 site’s SEO, performance, and social media presence. It contains metadata that instructs browsers, search engines, and social platforms on how to handle your content. While Joomla excels at managing basic metadata like <title> and <meta name="description">, it lacks native support for advanced features like OpenGraph, Twitter Card tags, and extended robots directives. This guide provides Joomla developers and site owners with the bare minimum <head> tags, favicon setup, social media metadata, and SEO-focused links, leveraging plugins like Route 66 and RicheyWeb’s Fields - XMLForm, System - Link Canonical, and System - Meta Robots to simplify implementation and enhance SEO control.

Four weeks ago, I rolled the dice on my Texas gun show listings site. Old event pages were choking search results, serving up outdated content and frustrating users. My fix? A white-hat SEO trick called the unavailable_after meta tag to deindex those pages after they expired. The result was a wild ride: a 70% traffic plunge, followed by a near-full recovery over four weeks as my upcoming events (re)took over the SERPs. Is this the SEO hack you’ve been missing? Here’s how I did it, why it might be working, and how you can test it.
Read more: unavailable_after White-Hat SEO Hack Might Be Paying Off
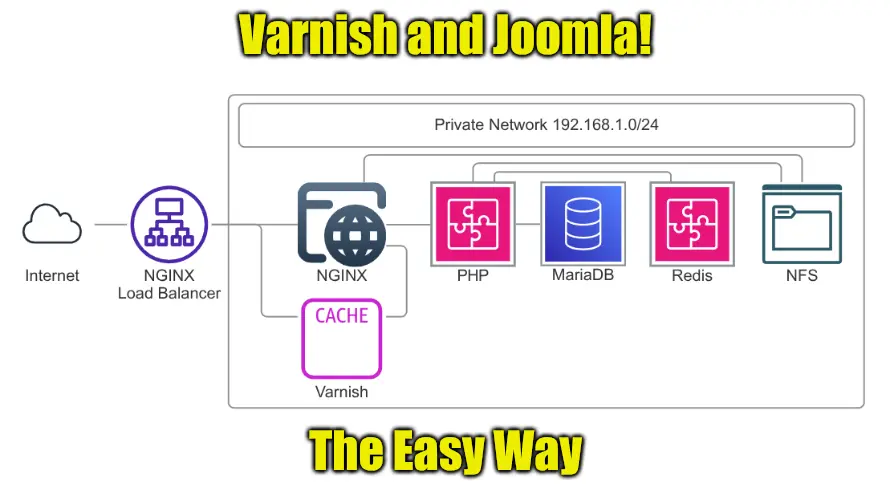
I made a statement in the Joomla forums offering to describe how I use Varnish and Joomla together. Well...today is the day! Due to an unforeseen summer cold - I'm not doing the outside work that I thought I'd be doing, so it's time to make good on that promise.

As a webmaster, I’ve been crushed by Microsoft Deliverability issues, with their S3140 error—“part of their network is on our block list”—blocking my RicheyWeb server’s 1–5 weekly emails to outlook.com, hotmail.com, live.com, and countless business domains hosted by Microsoft.
Read more: Microsoft Deliverability - SendGrid and Blacklists

Staying ahead of the content game is tough. Whether you’re a blogger, marketer, or niche website owner, sifting through news, trends, or industry updates to find relevant topics can feel like searching for a needle in a haystack. Manual research eats up hours, and by the time you spot a hot topic, it’s often too late to capitalize. Enter AI automation—a smarter way to discover content opportunities that drive traffic, engagement, and revenue.
You know the drill: hosting life means sifting through 404 logs like a digital archaeologist. This week’s find? Thousands of bots clawing at my server for phpinfo.php in every directory they could dream up—most of which don’t even exist. My usual move? Redirect those suckers straight to an FBI hate crime database download. It’s my little “get lost” postcard—funny, sure, but that’s just the warm-up.
Read more: Hacking phpinfo()? More Like a Free Ticket to the FBI’s Inbox
I had an interesting interaction this week that I thought might make a good article. It all started with a bounced email.
Anyone paying attention to my AdminExile graph on the homepage will notice that for the past few days there is a ~200 attempt spike in the attempts to access /administrator on this site.